Cybersecurity - Protecting systems, networks, and data from digital attacks and unauthorized access.
Loading...
More »










Popular Posts

Innovations in Visual Storytelling

Creating a Culture of Smart Learning in Schools
Embracing Change in Graphic Design

Innovative Teaching Methods for Modern Classrooms

The Impact of Robotics in Medicine

The Future of Robotics in Surgery
Common Myths About Open Source
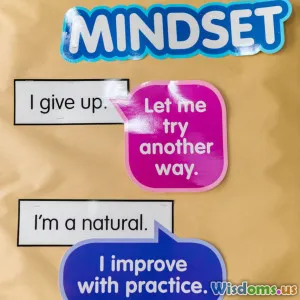
Strategies for Lifelong Learning

Navigating the World of Open Source Projects

Navigating AI: Insights from Science Fiction
Categories »