Database Backup Strategies Every IT Professional Should Know
25 min read Essential database backup strategies for IT pros, covering full, differential, incremental methods, RPO/RTO planning, 3-2-1 rule, encryption, automation, cloud and on‑prem, and restore testing. (0 Reviews)
You can lose a database in seconds; rebuilding trust with your users can take months. That stark reality is why backup strategy is not a box-ticking exercise but a design discipline. Whether you run a small SaaS on Postgres or a global estate with Oracle, SQL Server, and MongoDB, mastering backup fundamentals—and the trade-offs behind them—is a core IT skill that pays off the day something goes wrong.
RPO and RTO: The compass for every decision

Two numbers should drive every backup choice:
- Recovery Point Objective (RPO): How much data loss (in time) is acceptable? Example: If your RPO is 15 minutes, your strategy must ensure you can restore to within the last 15 minutes (e.g., frequent log/WAL backups or continuous archiving).
- Recovery Time Objective (RTO): How quickly must service be restored? Example: If your RTO is 30 minutes, full data rehydration from slow cold storage will not cut it—you’ll need faster tiers or ready standbys.
Practical examples:
- A fintech trading system might set RPO = 1 minute and RTO = 5 minutes—driving use of synchronous replication plus transaction log backups.
- An internal reporting system might accept RPO = 24 hours and RTO = 4 hours—suitable for nightly fulls with weekly differentials.
Tip: Write RPO/RTO into a short service-level document. Tie them to measurable checks: log backup frequency, restore drill timing, and maximum snapshot lag.
Backup types and when to use them
Not all backups are equal. Choosing correctly makes restores faster, cheaper, and less disruptive.
- Full backups: A self-contained copy of the entire database at a point in time. Best for weekly baselines or small databases. Pro: simple restores. Con: largest size and window.
- Incremental backups: Capture only changes since the last backup of any type. Great for daily or hourly cycles. Pro: small and fast. Con: restore chains can be long.
- Differential backups: Capture changes since the last full backup. Pro: restore chain is short (full + latest differential). Con: size grows until the next full.
- Transaction log/WAL/redo backups: Continuous stream of changes; enable point-in-time recovery (PITR). Pro: excellent RPO. Con: requires careful management and testing.
- Logical vs physical:
- Logical (e.g., mysqldump, pg_dump): Portable across versions, useful for migrations and partial restores (single schema/table). Con: slower, larger.
- Physical (e.g., pg_basebackup, Percona XtraBackup): Faster and consistent file-level copies; good for large production. Con: version-specific, less granular restore.
- Snapshots: Storage- or VM-level point-in-time copies. Pro: very fast creation for short RPO/RTO, especially with copy-on-write arrays and cloud snapshots. Con: must ensure application consistency (quiescing); crash-consistent snapshots alone can be risky for active databases.
Actionable pairing examples:
- High-change OLTP Postgres: nightly physical full + continuous WAL archiving; optionally hourly storage snapshots for fast rollbacks.
- Read-heavy SQL Server: weekly full + daily differential + 15-minute log backups; use backup compression.
- MongoDB: periodic filesystem snapshots coordinated via fsyncLock/fsyncUnlock or Ops Manager, plus frequent oplog capture.
The 3-2-1 rule (and its modern variants)

The classic: Keep 3 copies of data, on 2 different media, with 1 offsite. Today’s threat landscape (ransomware, insider risk) has evolved the rule:
- 3-2-1-1-0: Three copies, two media, one offsite, one immutable/air-gapped copy, and zero unverified backups (i.e., every backup is tested).
- Immutability/WORM:
- AWS S3 Object Lock (compliance or governance mode)
- Azure Immutable Blob Storage (time-based retention or legal hold)
- Google Cloud Bucket Lock
- Air gap: Physically or logically isolate at least one copy (e.g., offline tape, separate backup account with MFA delete).
Example policy: Primary in production, secondary in a backup repository, tertiary immutable copy in a different cloud region with Object Lock and cross-account ownership.
Consistency: from crash-consistent to application-consistent

Your backups are only as good as their consistency guarantees.
- Crash-consistent: Equivalent to pulling the power cord. Databases usually recover from logs on restart, but you risk torn pages or lost in-flight transactions.
- Application-consistent: The database is quiesced, checkpoints flushed, and I/O paused or coordinated, ensuring a clean state for snapshots or file copies.
How to achieve application consistency:
- Postgres: Use pg_basebackup or pgBackRest; enable WAL archiving. For storage snapshots, use pg_start_backup/pg_stop_backup (legacy) or replication slots/backup tools that coordinate safe points; verify with pg_verifybackup on newer versions.
- MySQL: Use Percona XtraBackup for hot physical backups. For logical snapshots, FLUSH TABLES WITH READ LOCK to coordinate, though this impacts writes; better is to use native hot backup tooling.
- SQL Server: Use native BACKUP commands. For VM snapshots, use VSS (Volume Shadow Copy Service) to freeze I/O; confirm application-consistent status in the hypervisor logs.
- Oracle: Use RMAN with BEGIN/END BACKUP for hot backups and archived redo log capture; coordinate storage snapshots with RMAN to avoid fractured blocks.
Rule of thumb: If a vendor supports an agent or native tool, prefer it over generic VM snapshots alone.
Engine-specific tactics: Postgres, MySQL, SQL Server, Oracle, MongoDB

Every engine has its own best practices. Skipping them is where many recovery stories go sideways.
PostgreSQL:
- Use pgBackRest or barman for orchestration, retention, compression, and WAL archival.
- Enable continuous archiving and test point-in-time recovery regularly.
- Example baseline script:
# Take a full backup with pgBackRest profile "main"
pgbackrest --stanza=main --type=full backup
# Confirm the backup is valid
pgbackrest --stanza=main check
- For large clusters, consider streaming replication to a hot standby plus regular backups; replication is not a backup, but it reduces RTO while backups cover corruption and deletion scenarios.
MySQL/MariaDB:
- Prefer Percona XtraBackup or MySQL Enterprise Backup for hot physical backups.
- Logical dumps (mysqldump or mydumper) are ideal for partial restores or migrations; they are slower and larger but highly portable.
- Ensure binary logs (binlog) are enabled and archived to meet RPO targets; use GTIDs for reliable recovery sequencing.
Microsoft SQL Server:
- Recovery models matter:
- Full: Needed for log backups and PITR.
- Simple: No log backups; best for non-critical or staging systems.
- Typical cadence: weekly full, daily differential, 15-minute log backups. Use WITH CHECKSUM and run RESTORE VERIFYONLY after each backup file is created.
- Consider Always On Availability Groups for HA, but keep independent backups—replication won’t save you from logical corruption.
Oracle Database:
- RMAN is the gold standard. Automate full and incremental (level 0/1) backups with archived redo logs.
- Use block change tracking to accelerate incrementals.
- Validate with RMAN RESTORE ... VALIDATE and crosscheck catalog.
MongoDB:
- For replica sets, take backups from secondaries to offload primaries, but ensure they are in sync.
- Use filesystem snapshots coordinated with fsyncLock/fsyncUnlock for consistency, or leverage Ops Manager/Atlas Backup for PITR.
- Archive the oplog for near-continuous recovery options.
Across engines: keep a backup catalog listing backup sets, timestamps, LSN/SCN ranges, and locations. This speeds up triage during a 2 a.m. recovery.
Cloud databases and managed services

Managed services simplify backups—but they don’t absolve you of design decisions.
- AWS RDS/Aurora:
- Automated backups with PITR (1–35 days retention by default). Create manual snapshots for long-term retention or pre-upgrade checkpoints.
- Cross-region automated backup copies for disaster recovery. Use KMS encryption and, for S3-based exports, enable S3 Object Lock.
- Azure SQL Database:
- Automated full/diff/log backups with PITR up to 35 days (longer with Long-Term Retention to up to 10 years). Geo-redundant backup storage optional.
- Google Cloud SQL:
- Automated backups with PITR for MySQL and Postgres; configure backup windows to avoid heavy workload times. Enable CMEK for encryption control.
- MongoDB Atlas:
- Cluster-wide backups with continuous cloud backup option; schedule snapshot frequency and retention tiers.
Maxim: Cloud snapshots are not strategy; they are a tool. Set RPO/RTO, choose retention, test restores into isolated staging projects, and protect accounts with separate IAM principals and alerting.
Designing a real-world backup plan: a how-to

Follow this blueprint to move from ad hoc backups to a resilient, auditable program.
- Profile your workloads
- Inventory databases: engine, version, size, growth rate, peak hours, dependencies.
- Classify data: regulatory needs (HIPAA, GDPR), PII handling, legal hold requirements.
- Set targets and patterns
- Define RPO/RTO per system; categorize into tiers (gold/silver/bronze).
- Choose backup patterns: e.g.,
- Gold (mission-critical): weekly full, daily differential, 15-minute logs, WAL/binlog archiving, immutable offsite copy, quarterly full restore drills.
- Silver: weekly full, daily incremental, hourly logs, monthly immutable snapshot.
- Bronze: nightly full to local repo, weekly offsite copy.
- Schedule intelligently
- Backup windows: avoid peak write periods. Consider change rates: a 1 Gbps link moves ~125 MB/s, or ~450 GB/hour; a 2 TB full will exceed a 4-hour window at that rate.
- Stagger jobs across systems to reduce I/O contention; cap concurrency by storage throughput.
- Retention and rotation
- Implement tiered retention (GFS model):
- Daily (sons): keep 7
- Weekly (fathers): keep 5
- Monthly (grandfathers): keep 12
- Yearly archives: keep 7
- Align retention with compliance mandates; document exceptions for right-to-erasure laws (GDPR) via legal hold process.
- Storage planning
- Estimate backup repository: Full size + (change rate × retention). Apply compression/dedupe ratios (2:1–4:1 typical, workload-dependent).
- Separate storage classes: hot (fast restores), cool/archive (long-term). Consider early deletion fees and retrieval times.
- Security and access
- Encrypt in transit and at rest. Store keys in KMS/HSM; rotate keys and test re-encryption procedures.
- Use least privilege: backup service accounts that can read data but cannot drop schemas.
- Maintain immutable offsite copies (Object Lock, WORM tape). Require MFA for deletion.
- Tooling and orchestration
- Prefer native database tools; integrate with enterprise backup platforms (e.g., Veeam, Commvault, Rubrik, Cohesity) where appropriate and with application-consistent hooks.
- Maintain a backup catalog and metadata index: backup IDs, timestamps, LSN/SCN ranges, checksum manifests.
- Test restores (non-negotiable)
- Automate verification: checksums, “verify only” commands, pg_verifybackup.
- Perform quarterly restore drills to realistic targets: spin up a clone, replay logs to a specified timestamp, validate application startup and critical queries.
- Time each drill; compare to RTO; document gaps and remediation.
- Document and train
- Create a one-page runbook per system: where backups live, last known good point, commands to restore, contacts, and on-call rotations.
- Conduct tabletop exercises: simulate accidental deletes and corruption; ensure DBAs and SREs are comfortable executing restores under time pressure.
Encryption, security, and immutability

Security failures often surface during recovery, when keys are missing or backups were quietly altered. Make security part of the design, not an afterthought.
- Encryption at rest:
- Database-native TDE (SQL Server, Oracle, some Postgres extensions) covers data files; confirm that backup files are also encrypted, or wrap them with backup-level encryption.
- Object storage encryption with KMS-managed keys; separate key admin roles from backup operators.
- Encryption in transit: Force TLS for backup traffic, especially between sites or to cloud.
- Immutability:
- Use WORM-capable storage (S3 Object Lock, Azure Immutable Blob). Set retention and legal hold where policy requires.
- Cross-account isolation: Store immutable copies in a separate account/project with limited trust and MFA for destructive actions.
- Integrity verification:
- Use backup checksums and verify operations (SQL Server WITH CHECKSUM; RMAN VALIDATE; pg_verifybackup; XtraBackup --prepare and verify phases).
- Maintain signed manifests (e.g., SHA-256) and store separately to detect tampering.
Bonus: Ransomware playbook—assume your primary and secondary repositories get encrypted. Your survival is the immutable copy plus tested recovery paths and network isolation during restore.
Testing, monitoring, and documentation

If you haven’t restored it, you don’t own it. Good teams invest in visibility.
- Proactive tests:
- Daily automated verify jobs (lightweight). Weekly sample restores of small databases. Quarterly full restores of tier-1.
- PITR drills: restore to a timestamp 7 hours ago; validate a report’s totals match historical values.
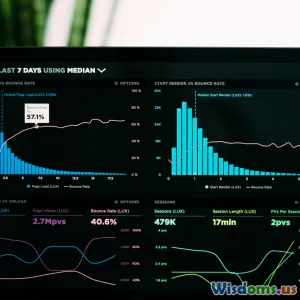
- Monitoring signals:
- Backup success/failure and duration vs usual baseline.
- Log/WAL backup age (alerts if > RPO threshold).
- Snapshot lag and replication health (if using standbys).
- Repository capacity and growth trends; alert at 70/85/95% thresholds.
- Documentation:
- Runbooks per engine with step-by-step restore procedures.
- Diagrams for data flows, security boundaries, and offsite paths.
- A catalog index searchable by date/time, database, and backup type.
Include a post-mortem template for any failed or delayed recovery; track action items to closure.
Performance and cost: practical trade-offs

Backups compete with production for I/O, CPU, and network. Tune or you’ll pay with slow apps and surprise bills.
- Compression:
- Often 2:1–4:1 on text-heavy databases; less on pre-compressed blobs.
- CPU-bound; schedule during off-peak or cap compression level to balance throughput.
- Deduplication:
- Great for incremental chains and repeated fulls. Inline dedupe appliances can shrink footprints dramatically but watch restore speed.
- Network:
- Throttle bandwidth to avoid saturating links; consider dedicated backup networks or QoS.
- For large offsite transfers, seed initial full to physical media or use cloud transfer services.
- Backup windows:
- Split databases by filegroups/tablespaces where supported; parallelize safe components.
- Use change block tracking (VM/array features) to reduce dirty block scanning.
- Restore speed tiers:
- Keep recent backups on fast disk for common incidents (accidental delete). Push long-term copies to cheaper storage; document retrieval SLAs.
Back-of-the-napkin math: Restoring 5 TB over 10 Gbps theoretical (~1.25 GB/s) is ~1.1 hours of data movement; real world is often half that due to overhead. If your RTO is 30 minutes, you need pre-warmed standbys or database-level replication coupled with fine-grained PITR.
Common failure modes and how to avoid them

The same mistakes recur in incident reviews. Guard against them early.
- Backups succeed, restores fail:
- Cause: No verification or corrupted media.
- Fix: Enforce verify jobs and periodic test restores; store checksums separately.
- Only VM snapshots, no application coordination:
- Cause: Belief that crash-consistent equals safe.
- Fix: Install agents or use native tools; integrate quiesce hooks.
- Missing transaction logs/WAL:
- Cause: Logs not archived or retention too short.
- Fix: Monitor log age; alert when retention headroom shrinks; test PITR.
- Backups encrypted with lost keys:
- Cause: Poor key management.
- Fix: KMS with rotation, break-glass procedure, and documented escrow.
- Replication mistaken for backup:
- Cause: Overreliance on HA.
- Fix: Maintain independent backups; corruption replicates instantly.
- Retention too short for latent corruption:
- Cause: Minimal storage budgets.
- Fix: Keep monthly/yearly restore points; scan for anomalies; consider logical checks (DBCC CHECKDB, pg_amcheck).
Create a “known-bad” playbook: if corruption appears, stop log shipping to secondaries to prevent poisoning all replicas.
Quick reference checklists
Daily
- Confirm previous night’s backups succeeded; review anomalies.
- Check log/WAL backup age against RPO.
- Validate repository free space and pending alerts.
Weekly
- Run sample restore in a sandbox; capture time to recover (TTR).
- Review job durations vs baseline; investigate deviations >20%.
- Cross-check backup catalog entries vs actual storage objects.
Monthly
- Full restore of at least one tier-1 database to a recovery environment; execute integrity checks and key application queries.
- Review and rotate credentials/keys as per policy.
- Audit immutability policies and offsite replication status.
Before major changes
- Create a manual snapshot/backup; label with change ID.
- Verify a clean restore path to pre-change state.
- Confirm team on-call coverage and runbook availability.
During incidents
- Freeze destructive automation (disable scheduled ETL deletes, suspend compaction if relevant).
- Triage scope: when did the issue start? Identify the last known good timestamp.
- Choose the lightest effective recovery (e.g., single-table logical restore vs full rollback).
Frequently asked questions from teams

- Do I still need backups if I run multi-AZ or Always On? Yes. Replication covers availability, not data integrity against deletions, bugs, or ransomware.
- Are snapshots enough? They can be, if they are application-consistent, retained appropriately, tested, and include offsite immutable copies. For complex databases, pair snapshots with native backups for safety.
- What’s a good starting cadence? For most production OLTP: weekly full, daily differential or incremental, 15-minute logs/WAL. Adjust based on change rates and SLAs.
- How long should I keep backups? As long as required by compliance and risk—commonly 30–90 days for operational restores, with monthly and yearly archives as part of GFS. Align with legal and privacy teams.
- How do I minimize downtime during restores? Keep recent backups on fast storage, maintain warm standbys, and practice surgical restores (e.g., filegroup/table-level or logical object restores) when supported.
A closing note on culture and ownership
Great backup strategies are the byproduct of great operational habits: writing down the RPO/RTO, picking fit-for-purpose tools, insisting on application consistency, rehearsing restores, and treating security as integral. The work feels routine—until the day it becomes heroic. If you establish these patterns now, you’ll turn data loss from an existential threat into a well-managed incident where your team knows exactly what to do and how fast they can do it.
Cloud Computing Information Technology Database Management Disaster Recovery IT Operations Database Administration Database backup strategies Full backup Differential backup Incremental backup Point-in-time recovery Snapshots RPO and RTO 3-2-1 backup rule Backup encryption Backup automation Cloud backups Offsite replication Retention policies Restore testing
Rate the Post
User Reviews
Popular Posts