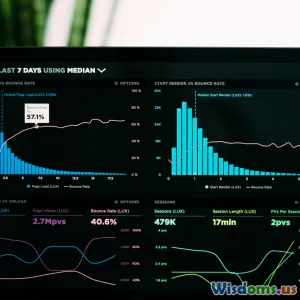
Track Website/Server Performance & Uptime 24/7 with Uptimer.us
29 min read Monitor websites, servers, ports, and game servers 24/7 with Uptimer.us. Heartbeats, SSL/domain renewals, DNS alerts, multi-location checks, custom HTTP, incidents, and instant email notifications. (0 Reviews)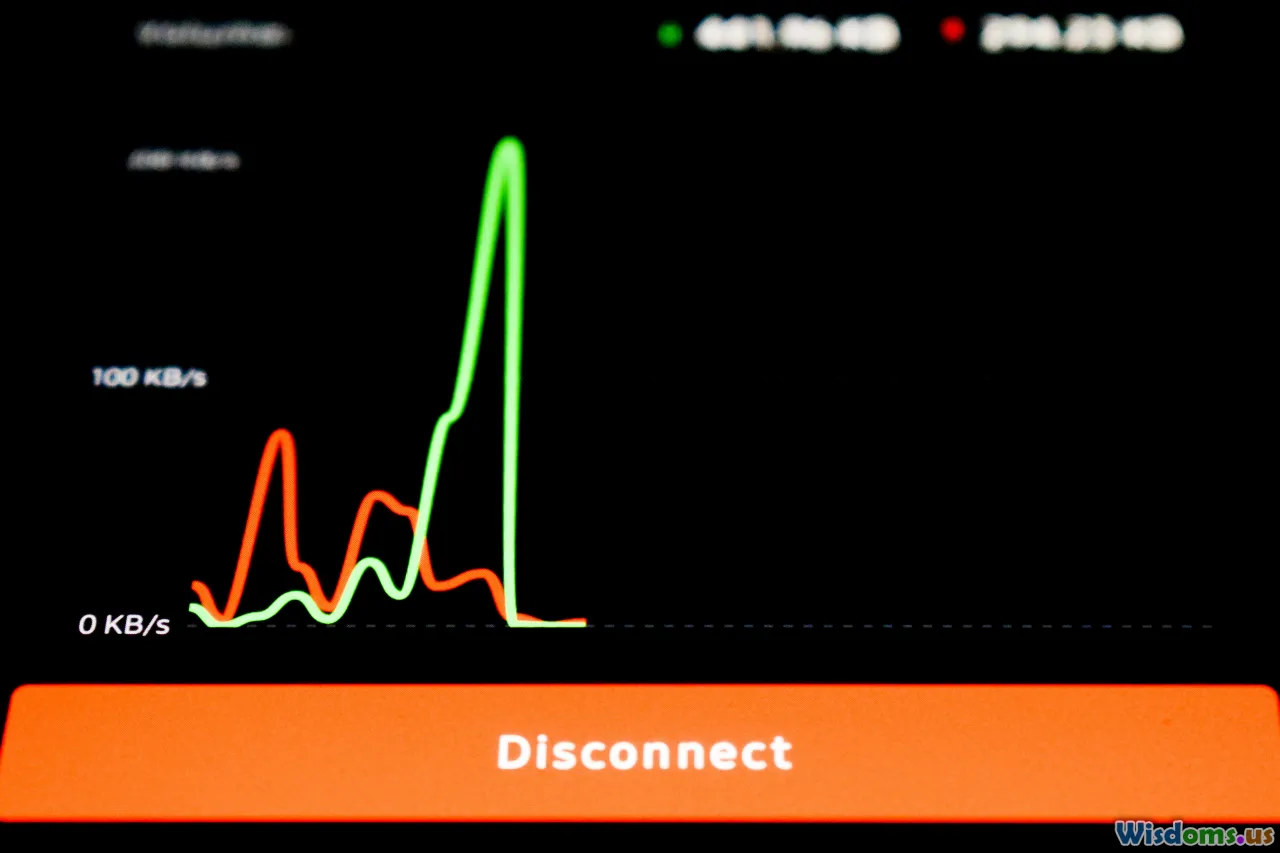
Keeping your site or service fast and available is no longer a nice-to-have; it underpins revenue, reputation, and reliability. Downtime erodes trust, latency damages conversion, and unmonitored changes cause surprises that are expensive to unwind. Whether you run a SaaS platform, an online game community, a content site, or internal business systems, the first step to staying in control is to observe them continuously. That is exactly what Uptimer.us delivers: always-on visibility, flexible checks, and actionable alerts that help you detect issues before users do.
Below, we’ll explore how Uptimer.us tracks websites, servers, ports, cron jobs, domains, SSL, DNS, and even game servers; how it correlates data from multiple locations; and how you can use custom requests, response expectations, and heartbeats to get signal-rich notifications without alert fatigue.
What makes 24/7 monitoring worth it
Monitoring is not just about catching downtime. It’s a way to quantify reliability and performance in business terms. Consider a few practical realities:
- A service that is 99.9% available (three nines) can still be down for over 43 minutes in a month. At scale, those minutes can coincide with peak traffic.
- Seemingly minor latency regressions compound. A difference of 300 ms on a checkout API across tens of thousands of requests can translate to meaningful abandonment.
- Most outages come from change: code deployments, DNS edits, expired SSL certs, or background jobs that quietly fail. Monitoring change is as crucial as monitoring uptime.
Uptimer.us is designed for this modern picture: it checks from multiple global vantage points, lets you tailor precise assertions for each check, monitors domain and SSL timelines, and ties alerts to meaningful triggers so you get notified for the right reasons.
A quick tour of Uptimer.us

Uptimer.us brings a broad toolset under one roof so you can monitor end-to-end:
- Website, server, and port monitors: Confirm HTTP(S) availability, API health, TCP port reachability, and network latency.
- Custom HTTP requests and responses: Build checks that mirror real traffic, add headers and auth, and assert exact outputs.
- Heartbeats: Verify that cron and scheduled tasks run on time and complete successfully.
- Domain and SSL tracking: Never miss renewal timelines for certificates or domain registrations.
- DNS monitors: Detect intended and unintended DNS changes as they happen.
- Game server checks: Track uptime, ping, online players, slots, and version for titles like Minecraft and Counter-Strike.
- Server resource monitors: Watch CPU, RAM, and disk usage on Linux, Windows, and macOS machines and trigger custom alerts.
- Incidents and alerts: Real-time notifications, custom failure triggers, multiple channels, and notes to document impact and fix.
- Multi-location checks: Validate from several regions to rule out local blips and find region-specific issues.
The result is a complete picture: service health, infrastructure capacity, change awareness, and clear timelines around issues.
How uptime checks work under the hood

Though it’s simple to set up, there’s a lot going on with each check:
- Probing from multiple locations: Monitors can be run from several geographic regions. If a service fails only in one region, you can differentiate a localized routing issue from a global outage.
- Interval-based scheduling: You choose the cadence for each check. More critical endpoints can be probed more frequently.
- Transport variety: Use HTTP(S) for websites and APIs, TCP for ports like 22 (SSH) or 5432 (PostgreSQL), and specialized queries for supported game servers.
- Adaptive insight: Each run captures status, response time, response size, and any assertion failures. This context shortens mean time to resolution (MTTR).
You get detailed history and uptime percentages over selectable windows. Over time, you’ll build a baseline that helps you recognize anomalies quickly.
Track websites, servers, and ports with ease
Reliable uptime monitoring starts with the essentials. Uptimer.us lets you create monitors for:
- HTTP and HTTPS endpoints: Perfect for landing pages, health endpoints, and REST APIs. Track status codes, TLS validity, response time, and content checks.
- TCP ports: Confirm services are accepting connections (e.g., 22 for SSH, 25 for SMTP, 443 for HTTPS offloaders, 3306 for MySQL). This is especially useful for internal services exposed via VPN or restricted networks.
- Host-level pings (where available): Quick verification of reachability and latency.
Practical examples:
- Monitor
https://example.comand assert a 200 status with a sub-500 ms median response time during business hours. - Check your mail relay at
mail.example.com:25to ensure your transaction emails won’t queue up. - Probe your staging API on a non-standard port and restrict alerts to your dev team.
Tip: Map checks to critical user paths. It’s better to monitor an authenticated health endpoint or a read-only API call used by users than an artificial ping that might keep passing while your app logic fails.
Flexible custom HTTP requests
Real applications require more than GET. With Uptimer.us you can:
- Select method: GET, POST, PUT, PATCH, DELETE, and more.
- Provide body: Send JSON or form data to mimic client requests.
- Add headers: Include
Authorization,Accept,Content-Type, and app-specific headers. - Use Basic Auth: Securely test endpoints protected by simple credentials.
- Control redirects: Follow or disallow redirects depending on your intent.
An actionable setup example:
- Endpoint:
https://api.example.com/health/deep - Method: POST
- Headers:
Content-Type: application/json,Authorization: Bearer <token> - Body:
{ "probe": "synthetic", "origin": "uptimer" }
This lets you exercise the same code paths that real clients use, catching regressions early. If your app expects an idempotent POST that performs checks and returns diagnostics, mirror that here.
Security tip: Use a limited-scope token for monitoring. If you rotate tokens, set a calendar reminder or automate via your secrets manager and update the monitor accordingly.
Precise custom HTTP responses and assertions

Monitoring is only as good as its signal. Uptimer.us supports layered expectations so checks fail for meaningful reasons:
- Status code: Require exact codes like 200, 201, 204, or a family like any 2xx.
- Header expectations: Verify headers exist or match patterns, e.g.,
Cache-Controlcontainsmax-age. - Body search: Require a string or regex like
"service":"ok"to appear. - JSON field asserts: If content is JSON, assert fields via simple paths, e.g.,
versionequals1.4.2ordependencies.databaseequalshealthy. - Performance thresholds: Fail the check if response time exceeds a target (for example, 800 ms) even if the status is 200.
Try a multi-assert pattern:
- Status equals 200.
Content-Typestarts withapplication/json.- JSON path
health.databaseequalsup. - Latency under 600 ms.
This catches slow, unhealthy, or misconfigured responses while filtering out transient network jitters.
Monitor cron jobs and scheduled tasks with heartbeats

Background jobs often fail silently. Heartbeats flip that script by having your job call a unique URL at start, success, and optionally on failure.
How to use heartbeats effectively:
- Create a heartbeat in Uptimer.us with an expected schedule, like every 15 minutes for a queue worker or nightly at 02:00 for a database backup.
- Add a simple call in your script at the end of a successful run:
curl https://uptimer.us/hb/<token>or use your language’s HTTP client. - Set a grace period for late completions (e.g., 5 minutes). If the ping doesn’t arrive in time, an incident triggers.
- Optionally, send a failure ping with an error summary if your job can trap exceptions.
Example jobs to monitor:
- Nightly backups, log rotations, and file archiving.
- ETL pipelines and report generation.
- Queue consumers that should never go idle.
Outcome: You’ll know exactly when a job began to fail, how late it ran, and whether it was intermittent or systemic.
Never miss SSL and domain renewals

Few things are as preventable as expired SSL certificates or lapsed domains. Uptimer.us tracks both timelines so you stay ahead.
- SSL monitoring: The platform checks certificate validity, issuer, subject alternative names (SANs), and time to expiration. Set reminders at multiple intervals so you get early, mid, and last-mile notices.
- Domain registration tracking: Receive alerts before registration lapses. This is vital if you manage many domains across different registrars.
Best practices:
- Aim to renew SSL 30 days before expiration to leave room for validation hiccups.
- For automated ACME renewals, still keep monitoring in place. Automation fails, and visibility is your safety net.
- Document registrar accounts and contact emails; alerts are only useful if they reach the right inboxes.
DNS monitors that catch intended and unintended changes

DNS changes are powerful and risky. A single A record edit can redirect traffic, break email, or degrade performance.
Uptimer.us can watch:
- A, AAAA, CNAME, MX, TXT, and other record types for your domain.
- Record values and TTLs for drift from your baseline.
- Changes over time with a log you can audit.
Use cases:
- Track a planned migration by setting a DNS monitor before the change window. Confirm that records flip as expected and that no stray updates happen later.
- Watch SPF or DKIM TXT records so email deliverability remains intact.
- Get alerted if an unexpected subdomain appears, which may indicate misconfiguration or unauthorized edits.
Tip: Pair DNS monitors with website and port checks during a migration. If DNS flips but your new targets aren’t ready, you’ll see it instantly.
Game server monitoring for communities and hosts

Running a game server means balancing performance and player experience. Uptimer.us supports popular titles like Minecraft and Counter-Strike, providing:
- Uptime and latency monitoring: Ensure the server is reachable and responsive.
- Online players and slots: Track current population relative to maximum slots to anticipate scaling needs.
- Server status and version detection: Verify you’re running the advertised version and detect mismatches after updates.
Example scenarios:
- A Minecraft community admin monitors player counts across weekends to spot trends and decide when to add capacity.
- A tournament host keeps an eye on a Counter-Strike server’s ping from multiple regions ahead of match time.
Insights from these checks flow into incidents just like other monitors, ensuring consistent alerting across your stack.
Server resource monitoring on Linux, Windows, and macOS

You can’t troubleshoot application slowdowns without visibility into the underlying machines. Uptimer.us can watch:
- CPU usage and load: Catch runaway processes or insufficient cores.
- RAM usage: Identify leaks and memory pressure before OOM kills occur.
- Disk usage: Prevent outages from full volumes or log growth.
- Custom usage alerts: Trigger incidents at thresholds you define, like CPU over 85% for 10 minutes.
A common rollout pattern:
- Start with baseline alerts: CPU > 80%, RAM > 80%, disk > 85%.
- Tune thresholds per server role, e.g., let batch nodes spike higher than interactive API nodes.
- Add per-volume alerts for disks that fill faster (like log or temp partitions).
Use the historical graphs to correlate resource spikes with deployments, traffic surges, or specific cron runs.
Incidents you can trust, alerts you can act on

Not all failures should trigger a page. Uptimer.us gives you fine control:
- Custom failed check triggers: Require N consecutive failures before an incident opens, or use a quorum across multiple locations (e.g., at least 2 locations must fail).
- Multiple channels at once: Send notifications to email and, if your workflow requires it, route to webhooks that fan out to chat or ticketing systems.
- Understand why it failed: See the last response, headers, latency, and any assertion that tripped. For TCP checks, see connection and timeout context.
- Leave notes for incidents: Record mitigation steps, root cause, and follow-up tasks. Notes help during handoffs and post-incident reviews.
Example: Your API has a 300 ms latency target. A deploy regresses median latency to 900 ms. With a performance threshold assertion, checks fail and open an incident. The alert includes the last few timings and the commit window, allowing a quick rollback and a post-mortem note.
Global multi-location validation reduces false positives

Network conditions vary. By running monitors from several regions, you can:
- Detect regional issues: If users in Europe report slowness, compare EU probe results to NA or APAC.
- Avoid false positives: Declare incidents only if multiple locations agree. A blip in one data center won’t wake up your team.
- Improve routing insights: Latency differences across regions can guide CDN changes or geographic failover plans.
Tip: Place probes where your users are. If 70% of your customers are in North America, ensure you include at least two NA locations so you can differentiate backbone issues from origin server problems.
Email notifications that are timely and readable

The best alert is the one you can parse quickly from a phone. Uptimer.us email notifications surface the essentials:
- Which monitor failed, where, and when.
- What changed or what assertion failed.
- A direct link to the incident timeline and graphs.
Reduce alert fatigue with these patterns:
- Use higher failure counts on less critical endpoints and lower counts for core APIs.
- Set maintenance windows so planned downtime doesn’t page you.
- Group related checks into one incident via conditions (e.g., if the upstream database is unreachable, API and site checks will fail; notify once with rich context).
How to get started in minutes
A simple setup path for a production website and API:
- Create an account at https://uptimer.us and add your first project.
- Add a website monitor:
https://yourdomain.com. Require status 200 and a content match likeWelcome. - Add an API monitor:
https://api.yourdomain.com/v1/health. Require 200, JSONokequalstrue, and response time under 500 ms. - Add a TCP port monitor for your database bastion or mail relay, such as
db-gateway.yourdomain.com:5432. - Create a heartbeat for your nightly backup job and paste the provided URL into the job’s success path.
- Enable domain and SSL tracking for your public domains and certs.
- Add DNS monitors for A and MX records of your root and subdomains.
- Choose 3 or more probe locations aligned to user distribution.
- Configure alerts: email to your on-call alias, plus optional webhook for your internal alert router. Set failure thresholds per monitor.
- Invite teammates and document runbooks via incident notes.
In under an hour, you’ll have coverage from uptime to resource usage, with change monitoring built in.
Smart ways to use custom requests and responses

Turn your monitors into living API contracts.
- Version pinning: Assert
x-api-versionheader equals your current release. If a CDN or proxy strips or alters it, you’ll catch the drift. - Canary behavior: Have a canary endpoint that exercises a dependency chain (cache, DB, third-party service). Fail the check if any link degrades.
- Partial degradations: Some services return 200 but with a degraded flag, e.g.,
{ "status": "degraded" }. Assert that status must beok. - Idempotent writes: For endpoints that accept POST but do not create persistent state, send a small payload and assert the echo. Keep payloads static and safe.
By including clear reasons in assertion messages, your alerts become self-explanatory: instead of generic 'check failed', they’ll read 'latency > 800 ms' or 'JSON health.database != up'.
Practical DNS and migration playbook

When planning a cutover:
- Before the window: Lower TTLs for A and CNAME records a few hours in advance so changes propagate faster.
- Add monitors: Create DNS, HTTP, and port checks for old and new targets side by side.
- During cutover: Flip DNS. Confirm that probes start hitting the new IP. Observe HTTP checks for regressions.
- Rollback plan: Keep the old infrastructure warm until new checks are green for a defined soak period.
- After cutover: Raise TTLs back to normal and keep DNS monitoring in place to catch unintended drifts.
This approach minimizes risk and provides proof of correctness at each step.
Tips to avoid alert fatigue while staying protected

- Use consecutive failure thresholds: A single timeout doesn’t need to wake you. Start with 2–3 consecutive failures.
- Differentiate criticality: Core payment and auth endpoints should alert immediately; marketing pages can wait for confirmation.
- Time-of-day awareness: Allow slightly higher latency thresholds during batch windows; tighten them during business hours.
- Group monitors by service: If a database outage cascades, open a single incident with attached checks.
- Regularly review stale monitors: Remove checks for retired endpoints and update assertion logic after major releases.
Who benefits from Uptimer.us

- DevOps and SRE teams: Reduce MTTR with context-rich incidents and multi-location confirmation.
- SaaS product teams: Treat performance as a feature and assert user-facing SLIs continuously.
- E-commerce: Watch checkout, payment callbacks, and email deliverability with API, port, and DNS checks.
- Game server admins and hosts: Keep communities happy by tracking uptime, ping, player counts, and versions.
- Agencies and MSPs: Monitor many clients in one place, standardize alerts, and show value with uptime history.
Security and privacy considerations

Monitoring touches production endpoints, so keep it safe:
- Limit credentials: Use Basic Auth or Bearer tokens with the narrowest scope needed for health checks.
- Avoid sensitive payloads: Use synthetic, non-production data in monitoring requests.
- TLS everywhere: Prefer HTTPS endpoints; certificate monitoring ensures you maintain strong encryption.
- Webhooks hygiene: If you use webhooks for alerts, restrict IPs or enforce secret validation on your receiving side.
- Access control: Invite only the necessary teammates and rotate credentials periodically.
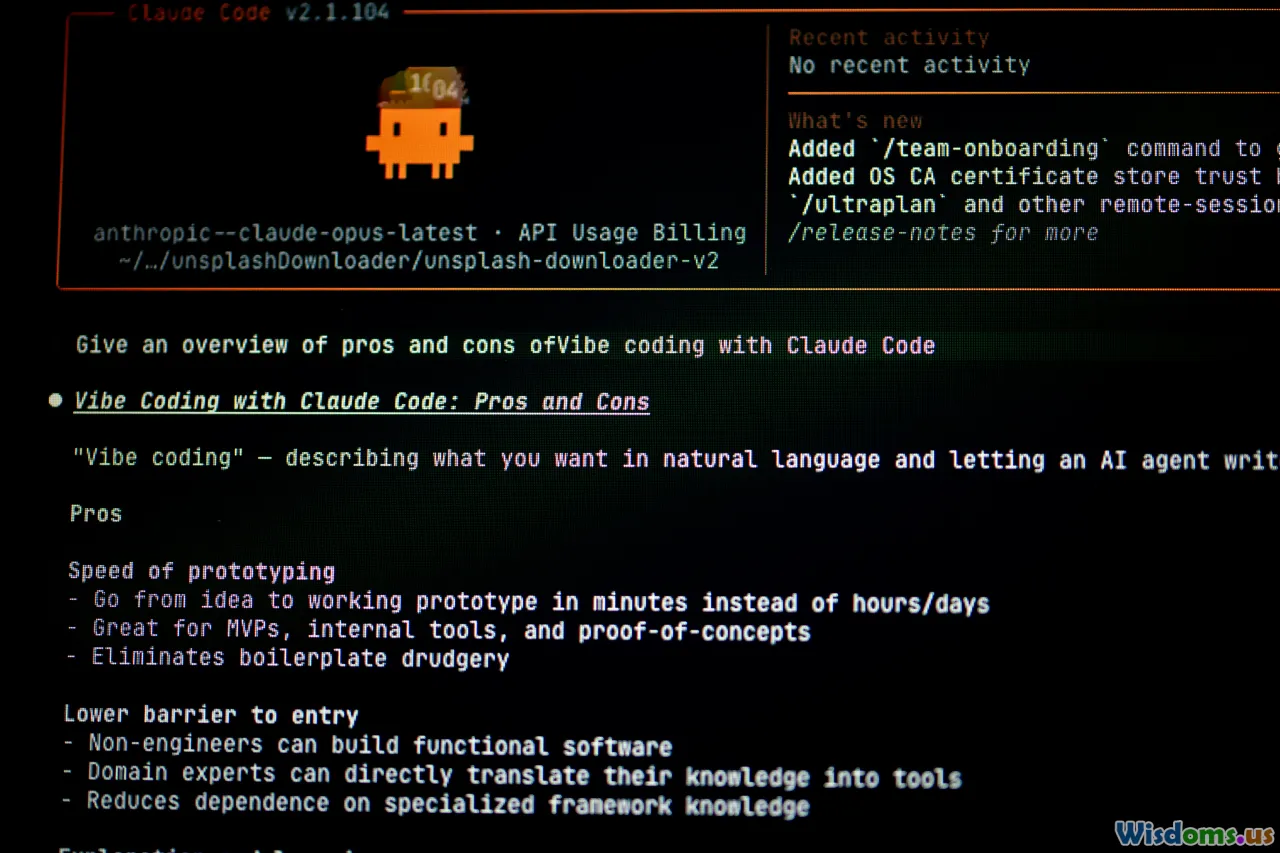
Why dedicated monitoring beats DIY scripts

Spinning up a cron that curls your site can work for a day. But over time, it falls short:
- Coverage: DIY often lacks DNS, SSL, domain, port, resource, and game server checks.
- Multi-location truth: A single vantage point can’t distinguish local from global issues.
- Signal vs. noise: Without assertions and thresholds, you either miss real problems or drown in false alarms.
- Incident workflow: DIY sends a message; it does not give timelines, notes, failure context, or grouped incidents.
- Maintenance: Scripts break, hosts go down, credentials drift. A managed platform maintains itself and evolves with your needs.
Uptimer.us centralizes these concerns so you can focus on product rather than plumbing.
Real-world example: Hardening an API-backed storefront

An online retailer saw sporadic checkout failures during peak demand. After deploying Uptimer.us:
- API monitor: Asserted 200 status and
paymentGatewayequalsavailablein JSON. Added a 500 ms latency threshold. - Port monitor: Verified TCP 443 on the payment proxy for early detection of TLS termination issues.
- Heartbeat: Confirmed nightly tax rate sync completed before opening hours.
- DNS monitor: Watched CNAMEs pointing to the CDN to catch an accidental edit.
- SSL tracking: Ensured the wildcard cert renewal happened ahead of a Black Friday freeze.
- Multi-location: Probes from NA and EU revealed that only EU shoppers experienced occasional slowdowns; a CDN routing tweak fixed it.
- Incident practice: Switched to two-consecutive-fail triggers on payment checks to page the on-call only when truly broken.
Within a week, the team cut false positives by 60% and caught a real provider-side blip before it turned into a widespread outage.
Your next step

Reliable services are built on visibility and fast feedback loops. With Uptimer.us, you get an always-on guardian for availability, performance, and change across websites, servers, ports, jobs, domains, DNS, and more. You can start small with a few essential checks and grow into precise, contract-level assertions as your system matures.
Create your first monitors today at https://uptimer.us, wire up heartbeats for critical tasks, and set thoughtful alert rules. The peace of mind you gain will pay for itself the next time a dependency blinks, a cert nears expiry, or a regional route goes sideways. Monitoring won’t stop issues from happening, but it will ensure you’re the first to know—and the fastest to fix.
DevOps Information Technology IT Support & Help Desk incident management Site Reliability Engineering Web Performance Optimization IT Monitoring Tools Website Uptime Monitoring Server Monitoring Port Monitoring Heartbeat Monitoring Cron Job Monitoring SSL Certificate Tracking Domain Expiration Alerts DNS Change Detection Game Server Monitoring Multi-Location Monitoring Custom HTTP Checks
Rate the Post
User Reviews
Popular Posts